1. Dictionary attack :-
"This uses a simple file containing words that can, surprise surprise, be found in a dictionary. In other words, if you will excuse the pun, this attack uses exactly the kind ofwords that many people use as their password..."
2. Brute force attack :-
"This method is similar to the dictionary attack but with the added bonus, for the hacker, of being able to detect non-dictionary words by working through all possible alpha-numeric combinations from aaa1 to zzz10..."
3. Rainbow table attack :-
"A rainbow table is a list of pre-computed hashes - the numerical value of an encrypted password, used by most systems today - and that’s the hashes of allpossible password combinations for any given hashing algorithm mind. The time it takes to crack a password using a rainbow table is reduced to the time it takes to look it up in the list..."
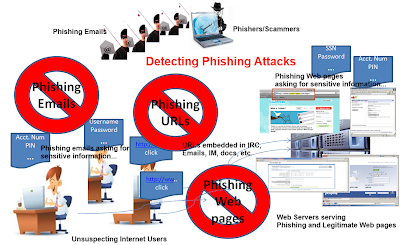
4. Phishing :-
"There's an easy way to hack: ask the user for his or her password. A phishing email leads the unsuspecting reader to a faked online banking, payment or other site in order to login and put rightsome terrible problem with their security..."
5. Social engineering :-
"A favourite of the social engineeris to telephone an office posing asan IT security tech guy and simply ask for the network access password. You’d be amazed how often this works. It take the advantage of people trust."
6. Malware :-
"A key logger or screen scraper can be installed by malware whichrecords everything you type or takes screen shots during a login process, and then forwards a copy of this file to hacker central..."
7. Offline cracking :-
"Often the target in question has been compromised via an hack ona third party, which then providesaccess to the system servers and those all-important user password hash files. The password cracker can then take as long as they need to try and crack the code without alerting the target system or individual user..."
8. Shoulder surfing :-
"The service personnel ‘uniform’ provides a kind of free pass to wander around unhindered, and make note of passwords being entered by genuine members of staff. It also provides an excellent opportunity to eyeball all those post-it notes stuck to the front of LCD screens with logins scribbled upon them..."
9. Spidering :-
"Savvy hackers have realised that many corporate passwords are made up of words that are connected to the business itself. Studying corporate literature, website sales material and even the websites of competitors and listed customers can provide the ammunition to build a custom word list to use in a brute force attack..."
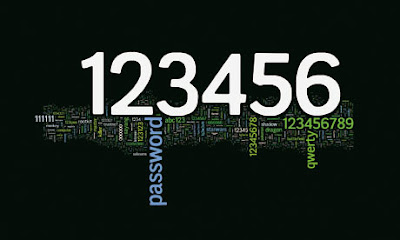
10. Guess :-
"The password crackers best friend, of course, is the predictability of the user. Unless a truly random password has been created using software dedicated to the task, a user generated ‘random’ password is unlikely to be anything of the sort..."















0 comments :
Post a Comment